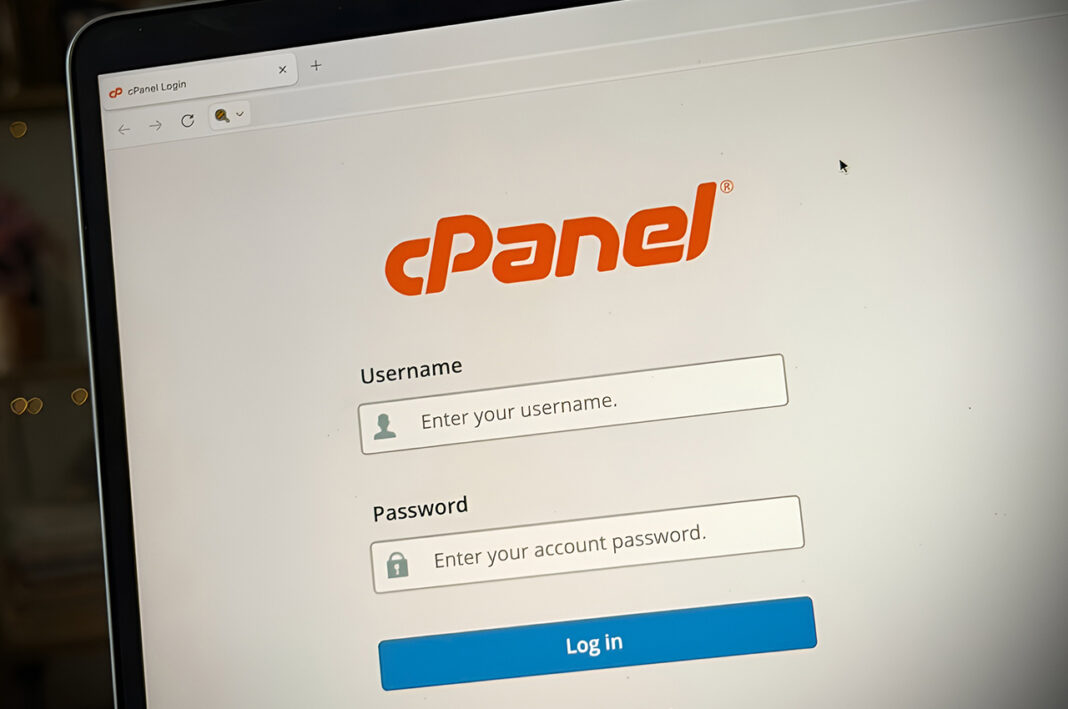
Hackers are actively exploiting a bug in cPanel, and millions of websites are exposed right now, in what cybersecurity experts are calling one of the most serious hosting vulnerabilities in recent years. The flaw is already being used in real-world attacks, putting businesses, government portals, and online services at immediate risk.
Key Development
A critical vulnerability in cPanel and its server management layer WHM has been identified and is now actively exploited by hackers worldwide.
The flaw, tracked as CVE-2026-41940, allows attackers to bypass login authentication entirely and gain administrative access without needing usernames or passwords.
This means attackers can:
- Take full control of hosting servers
- Access all websites hosted on those servers
- Steal sensitive data including user information
- Inject malware or ransomware
- Delete or disrupt entire websites
Security researchers warn that the vulnerability carries a severity score of 9.8 out of 10, making it one of the highest-risk bugs currently affecting the internet.
The issue affects all supported versions of cPanel and WHM after version 11.40, meaning a vast number of systems are potentially exposed.
Why It Matters
The scale of the vulnerability is what makes it particularly alarming.
cPanel is one of the most widely used web hosting platforms globally, powering:
- Small business websites
- E-commerce stores
- Government and institutional portals
- Media and content platforms
Security experts estimate that over a million internet-facing cPanel instances exist, many of which could be vulnerable if not patched.
For businesses in the UAE and Gulf region:
- Websites could be silently compromised without warning
- Customer data may be exposed or stolen
- Online services could face downtime or defacement
- Brand trust and financial losses could follow
The vulnerability essentially acts as a master key to hosting environments, making it a high-value target for cybercriminals.
Bigger Picture
The cPanel exploit highlights a growing trend in cybersecurity, where attackers are targeting infrastructure rather than individual websites.
Instead of hacking one site at a time, attackers:
- Compromise hosting servers
- Gain access to hundreds or thousands of websites at once
- Deploy large-scale attacks including botnets and ransomware
Recent reports indicate:
- Exploitation began even before public disclosure
- Tens of thousands of compromised systems were already scanning for new targets
- Multiple hacking groups are now weaponising the vulnerability
This type of attack is particularly dangerous for shared hosting environments, where a single breach can affect many unrelated businesses.
For fast-growing digital economies like the UAE, where SMEs rely heavily on online presence, such vulnerabilities pose a serious operational risk.
What Happens Next
A security patch has already been released, but the race between attackers and system administrators is ongoing.
Key actions being taken globally include:
- Hosting providers rushing to deploy emergency patches
- Temporary shutdown or restriction of cPanel access in some cases
- Increased monitoring for suspicious activity
- Urgent security advisories issued to customers
However, risks remain for:
- Websites running outdated versions
- Servers not yet patched
- Businesses unaware of the vulnerability
Experts strongly recommend immediate updates, password resets, and security audits.
As cyber threats continue to evolve, this incident may lead to:
- Stricter hosting security standards
- Greater adoption of managed security services
- Increased awareness among businesses about infrastructure risks
FAQs
What is the cPanel vulnerability?
It is a critical authentication bypass flaw that allows hackers to access servers without login credentials.
How serious is this bug?
It has a severity score of 9.8 out of 10 and is actively being exploited.
Who is at risk?
Any website hosted on vulnerable cPanel or WHM servers.
Has a fix been released?
Yes, but systems must be updated immediately to stay protected.
What should businesses do now?
Update systems, monitor activity, and consult hosting providers for security checks.Hackers are actively exploiting a bug in cPanel, and millions of websites are exposed right now, in what cybersecurity experts are calling one of the most serious hosting vulnerabilities in recent years. The flaw is already being used in real-world attacks, putting businesses, government portals, and online services at immediate risk.
Key Development
A critical vulnerability in cPanel and its server management layer WHM has been identified and is now actively exploited by hackers worldwide.
The flaw, tracked as CVE-2026-41940, allows attackers to bypass login authentication entirely and gain administrative access without needing usernames or passwords.
This means attackers can:
- Take full control of hosting servers
- Access all websites hosted on those servers
- Steal sensitive data including user information
- Inject malware or ransomware
- Delete or disrupt entire websites
Security researchers warn that the vulnerability carries a severity score of 9.8 out of 10, making it one of the highest-risk bugs currently affecting the internet.
The issue affects all supported versions of cPanel and WHM after version 11.40, meaning a vast number of systems are potentially exposed.
Why It Matters
The scale of the vulnerability is what makes it particularly alarming.
cPanel is one of the most widely used web hosting platforms globally, powering:
- Small business websites
- E-commerce stores
- Government and institutional portals
- Media and content platforms
Security experts estimate that over a million internet-facing cPanel instances exist, many of which could be vulnerable if not patched.
For businesses in the UAE and Gulf region:
- Websites could be silently compromised without warning
- Customer data may be exposed or stolen
- Online services could face downtime or defacement
- Brand trust and financial losses could follow
The vulnerability essentially acts as a master key to hosting environments, making it a high-value target for cybercriminals.
Bigger Picture
The cPanel exploit highlights a growing trend in cybersecurity, where attackers are targeting infrastructure rather than individual websites.
Instead of hacking one site at a time, attackers:
- Compromise hosting servers
- Gain access to hundreds or thousands of websites at once
- Deploy large-scale attacks including botnets and ransomware
Recent reports indicate:
- Exploitation began even before public disclosure
- Tens of thousands of compromised systems were already scanning for new targets
- Multiple hacking groups are now weaponising the vulnerability
This type of attack is particularly dangerous for shared hosting environments, where a single breach can affect many unrelated businesses.
For fast-growing digital economies like the UAE, where SMEs rely heavily on online presence, such vulnerabilities pose a serious operational risk.
What Happens Next
A security patch has already been released, but the race between attackers and system administrators is ongoing.
Key actions being taken globally include:
- Hosting providers rushing to deploy emergency patches
- Temporary shutdown or restriction of cPanel access in some cases
- Increased monitoring for suspicious activity
- Urgent security advisories issued to customers
However, risks remain for:
- Websites running outdated versions
- Servers not yet patched
- Businesses unaware of the vulnerability
Experts strongly recommend immediate updates, password resets, and security audits.
As cyber threats continue to evolve, this incident may lead to:
- Stricter hosting security standards
- Greater adoption of managed security services
- Increased awareness among businesses about infrastructure risks
FAQs
What is the cPanel vulnerability?
It is a critical authentication bypass flaw that allows hackers to access servers without login credentials.
How serious is this bug?
It has a severity score of 9.8 out of 10 and is actively being exploited.
Who is at risk?
Any website hosted on vulnerable cPanel or WHM servers.
Has a fix been released?
Yes, but systems must be updated immediately to stay protected.
What should businesses do now?
Update systems, monitor activity, and consult hosting providers for security checks.